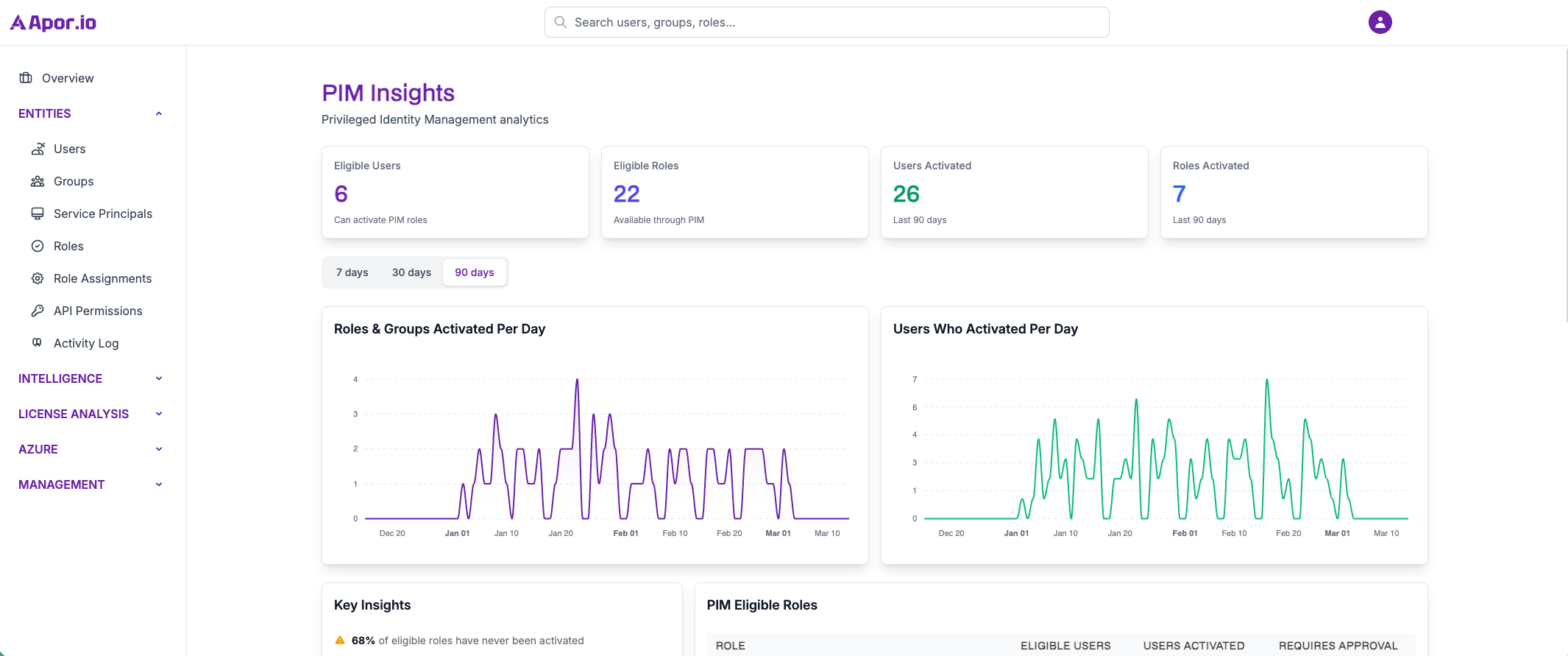
PIM Activity
Monitor and analyze Privileged Identity Management activities. Track role activations and privileged access patterns.
Role Activation Tracking
Monitoring of privileged role activations and duration
Privileged Access Analytics
Pattern analysis and detection for privileged users
Compliance Reporting
Audit trails for privileged access governance
Ready to Govern Privileged Access?
Join the waitlist to be the first to access comprehensive PIM activity monitoring and ensure proper governance of your privileged identities.
Join Waitlist Now