Complete Identity Intelligence Platform
Everything you need to discover, analyze, and secure identities across your Microsoft Entra ID environment.
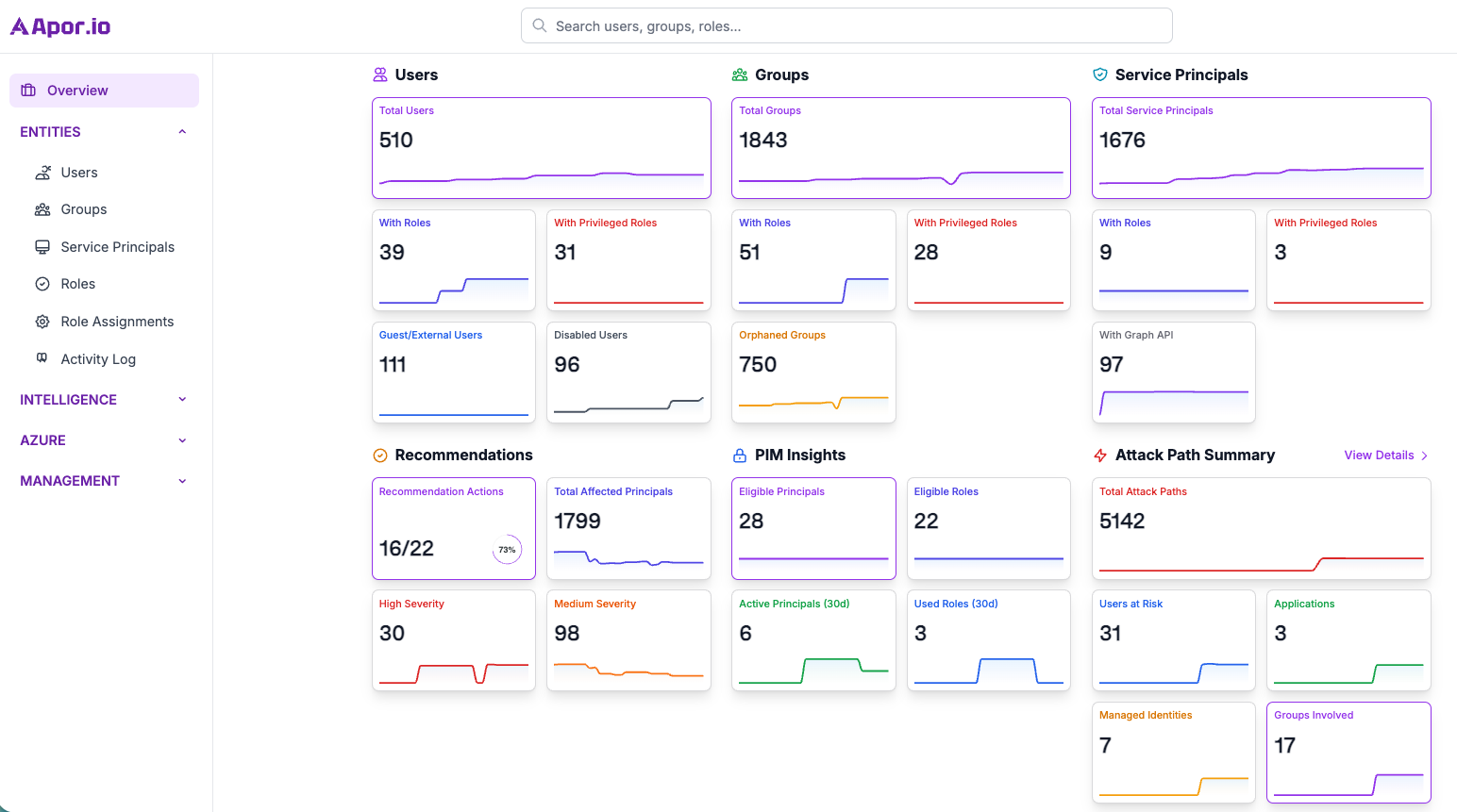
Overview Dashboard
Get instant visibility into your identity security posture within Entra ID with automated metrics and risk indicators.
-
Centralized Command Center
Core identity and security metrics at a glance
-
Identity Risk Overview
Critical privilege exposures and high-risk insights
-
Executive Reporting
High-level insights for stakeholders
Identity Discovery
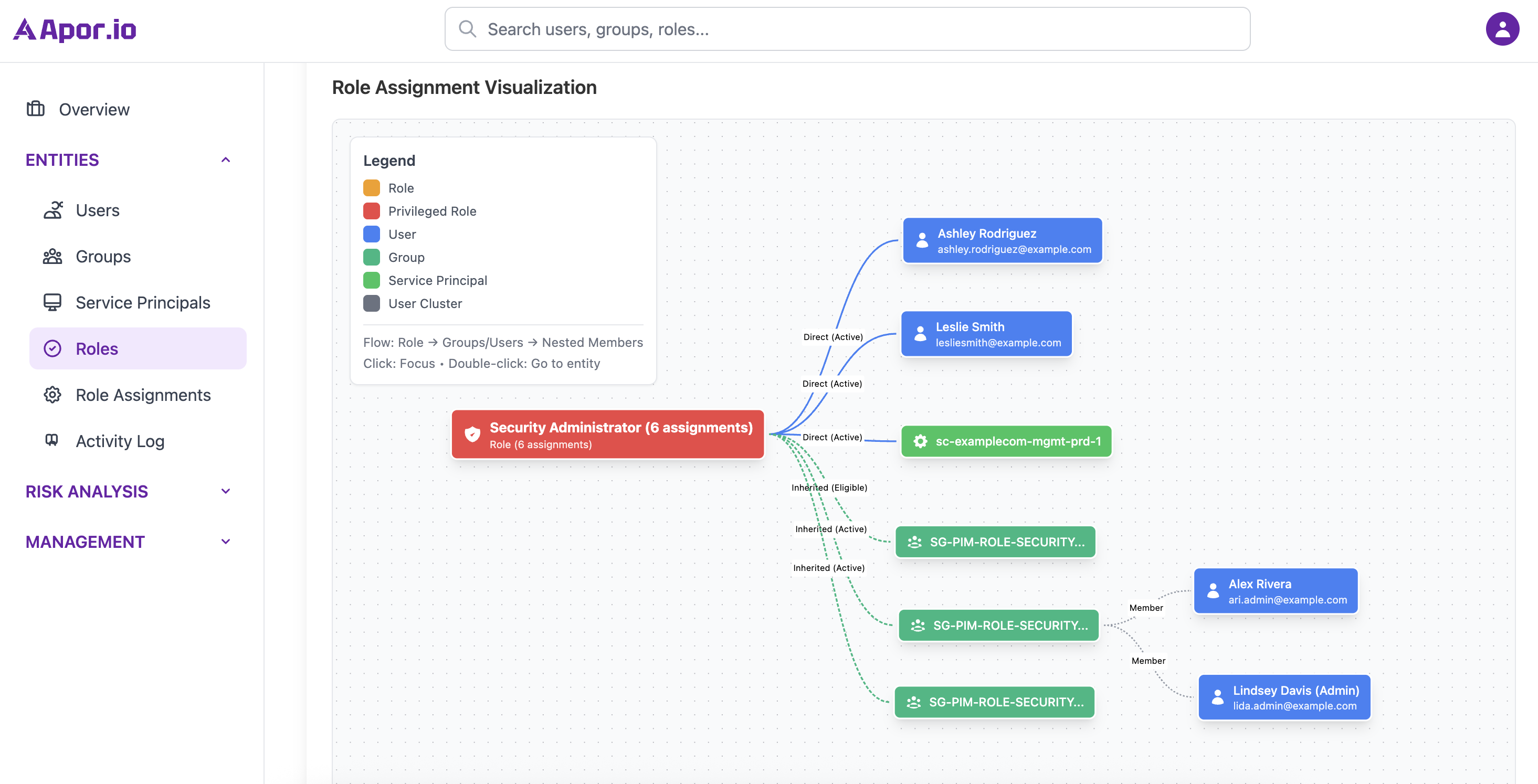
Automatically discover and map all identities, roles, and permissions across your Microsoft Entra ID environment.
-
Complete Identity Inventory
Map all users, groups, roles, and service principals
-
Permission Analysis
Deep dive into role assignments and inheritance
-
Risk Assessment
Identify high-risk accounts and privileged access issues
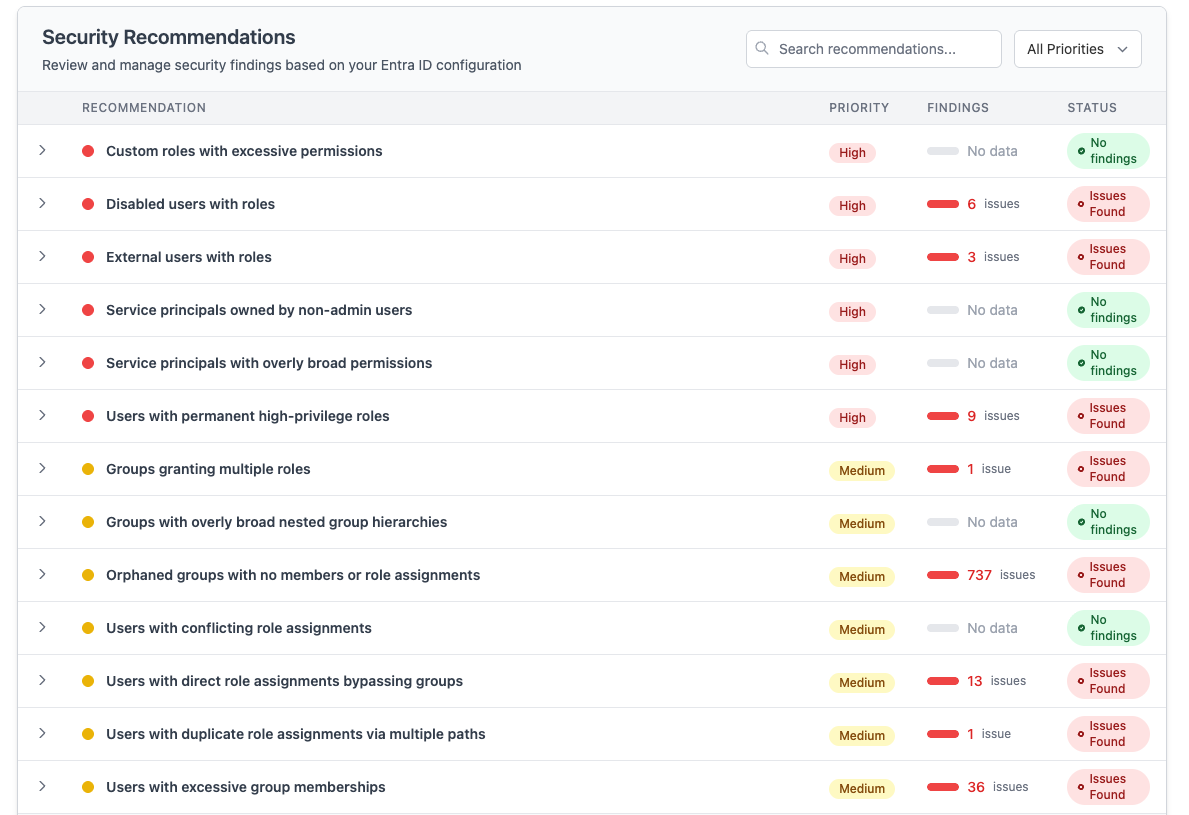
Security Findings
Get prioritized security recommendations tailored to your Microsoft Entra ID environment.
-
Automated Security Assessment
Continuous analysis of your identity security configuration
-
Prioritized Recommendations
Risk-scored findings ranked by security impact
-
Impact Analysis
Understand the business impact of security gaps
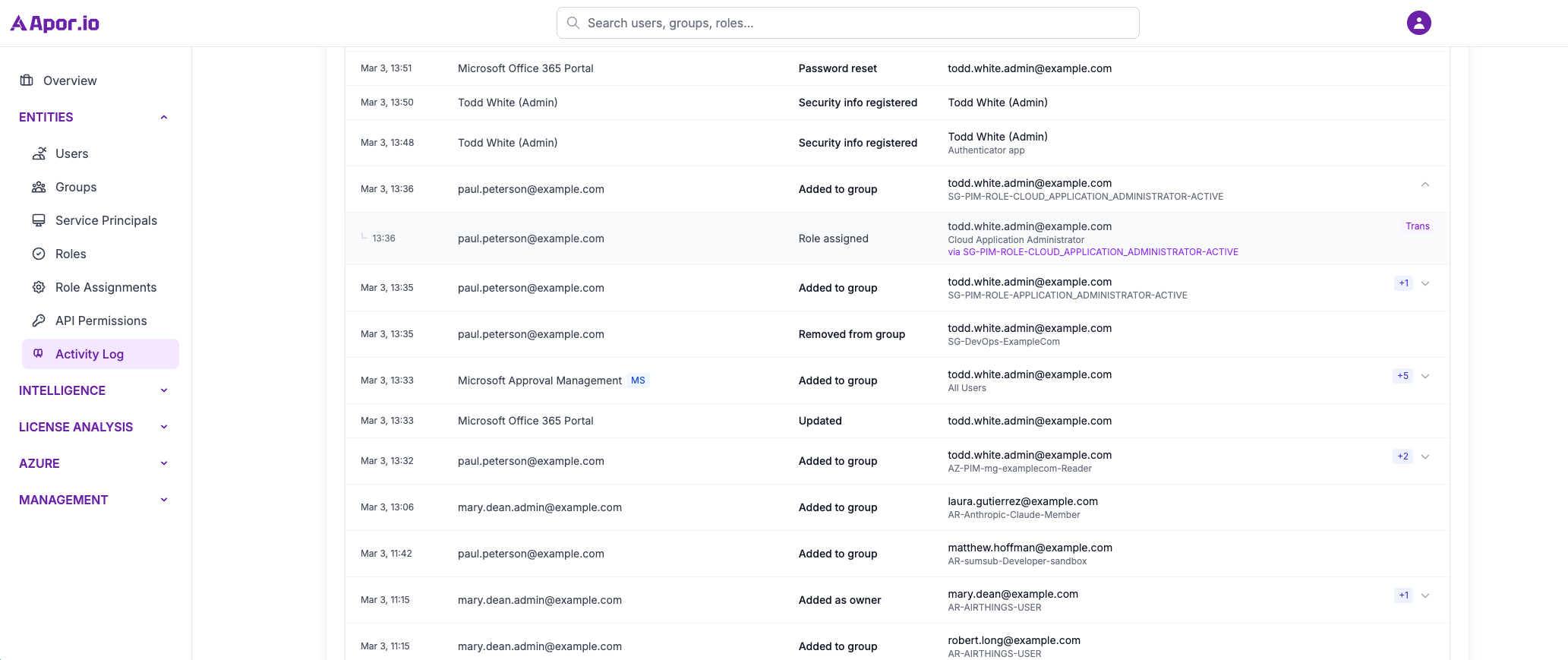
Change Tracking
Automatically capture and document all modifications to identities, roles, and permissions.
-
Automated Recording
Replace manual tracking with automated permission monitoring
-
Timestamped Audit Trails
Complete lifecycle event documentation
-
Infinite History
Long-term data retention for comprehensive auditing
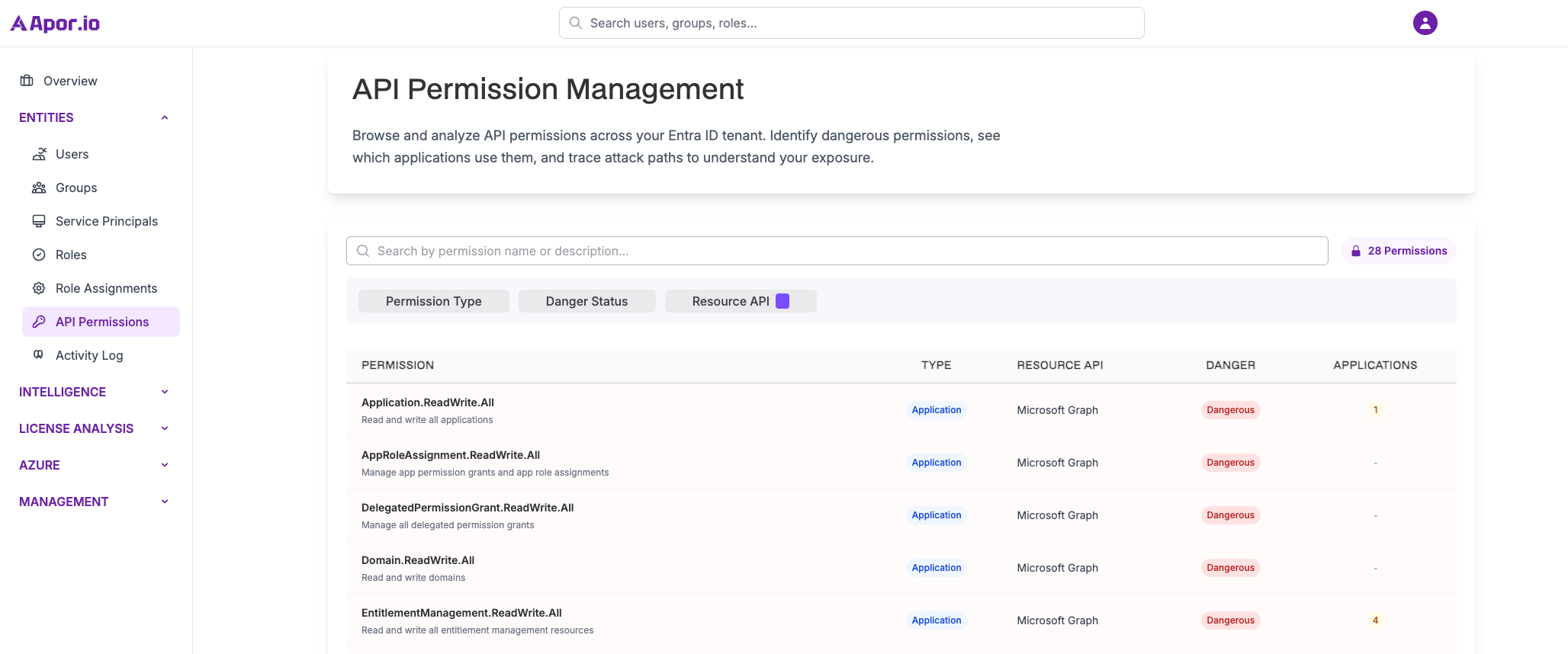
MS Graph Permission Analysis
Comprehensive analysis of Microsoft Graph API permissions across your service principals.
-
Permission Mapping
Complete inventory of Graph API permissions granted to applications
-
Risk Assessment
Automated identification of high-risk and excessive permissions
-
Compliance Reporting
Detailed reports for security audits and compliance reviews
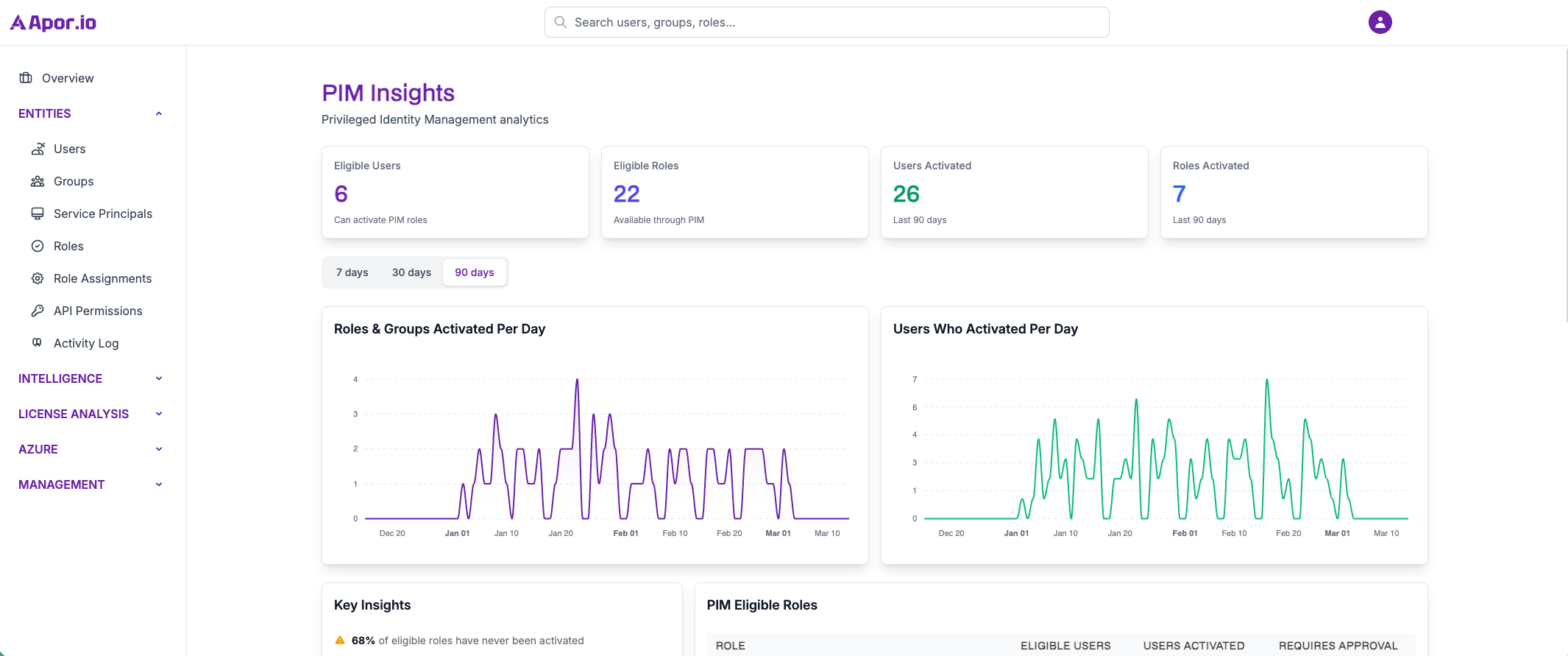
PIM Activity
Monitor and analyze Privileged Identity Management activities. Track role activations and privileged access patterns.
-
Role Activation Tracking
Monitoring of privileged role activations and duration
-
Privileged Access Analytics
Pattern analysis and detection for privileged users
-
Compliance Reporting
Audit trails for privileged access governance
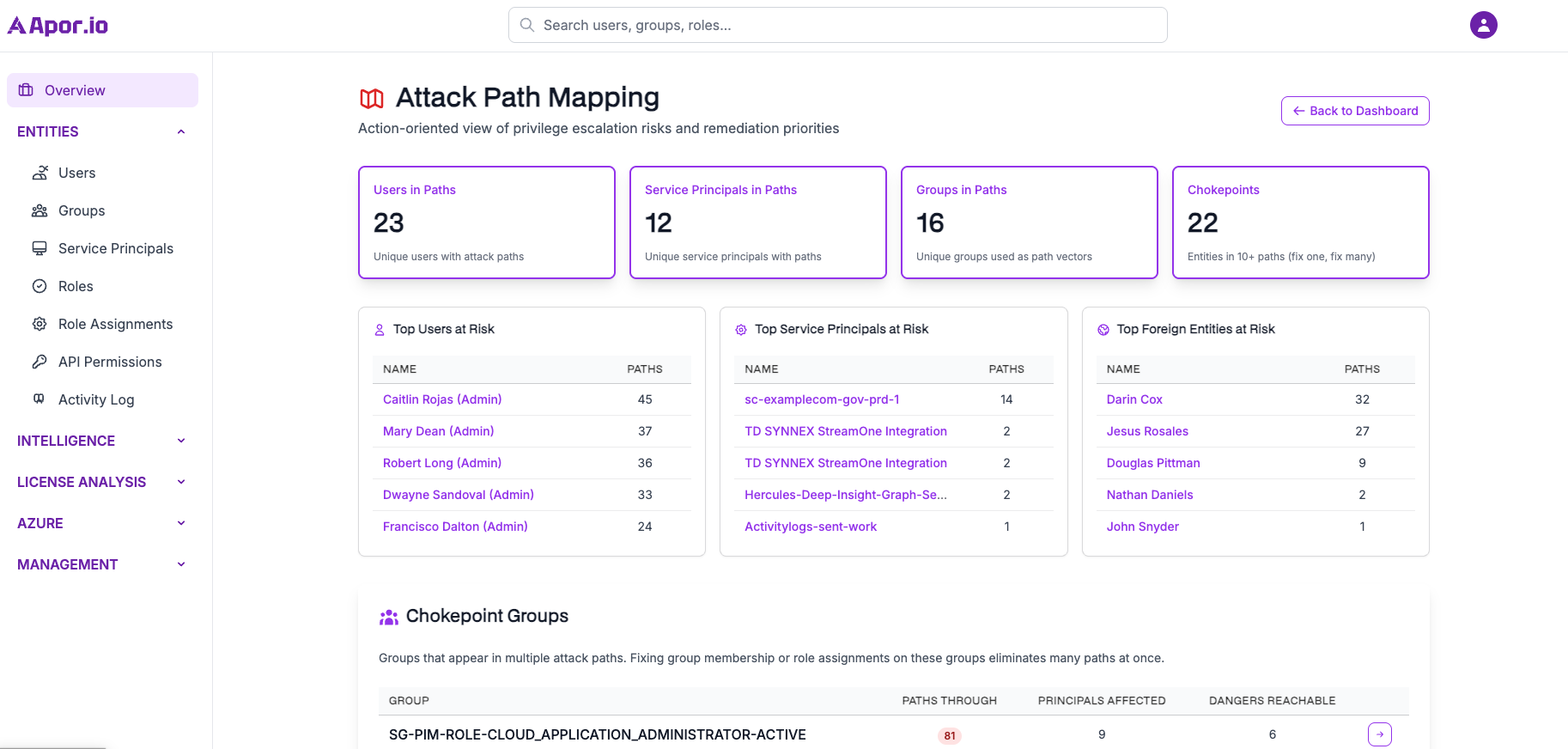
Attack Path Mapping
Visualize potential attack paths through your Entra ID environment. Identify privilege escalation routes before attackers do.
-
Visual Attack Paths
Interactive graph visualization of potential attack routes
-
Privilege Escalation Detection
Automated identification of escalation opportunities
-
Risk Prioritization
Critical path analysis and remediation prioritization
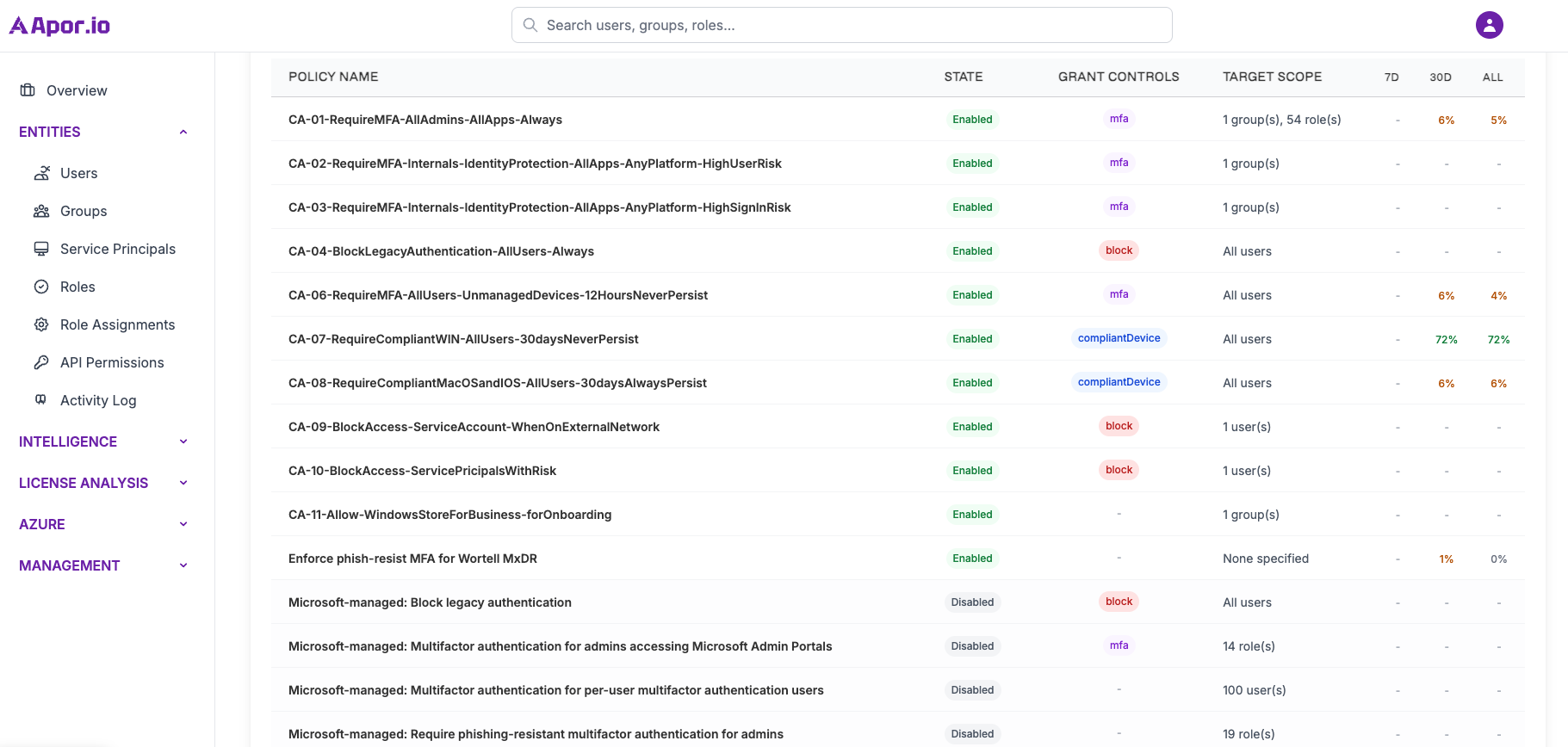
Conditional Access
Gain complete visibility over your Conditional Access policies. Understand configurations, assignments, and security impact.
-
Policy Visualization
Clear overview of all policies, assignments, and controls
-
Risk Assessment
Identify policy gaps and security vulnerabilities
-
Impact Analysis
Understand who is affected by policy changes
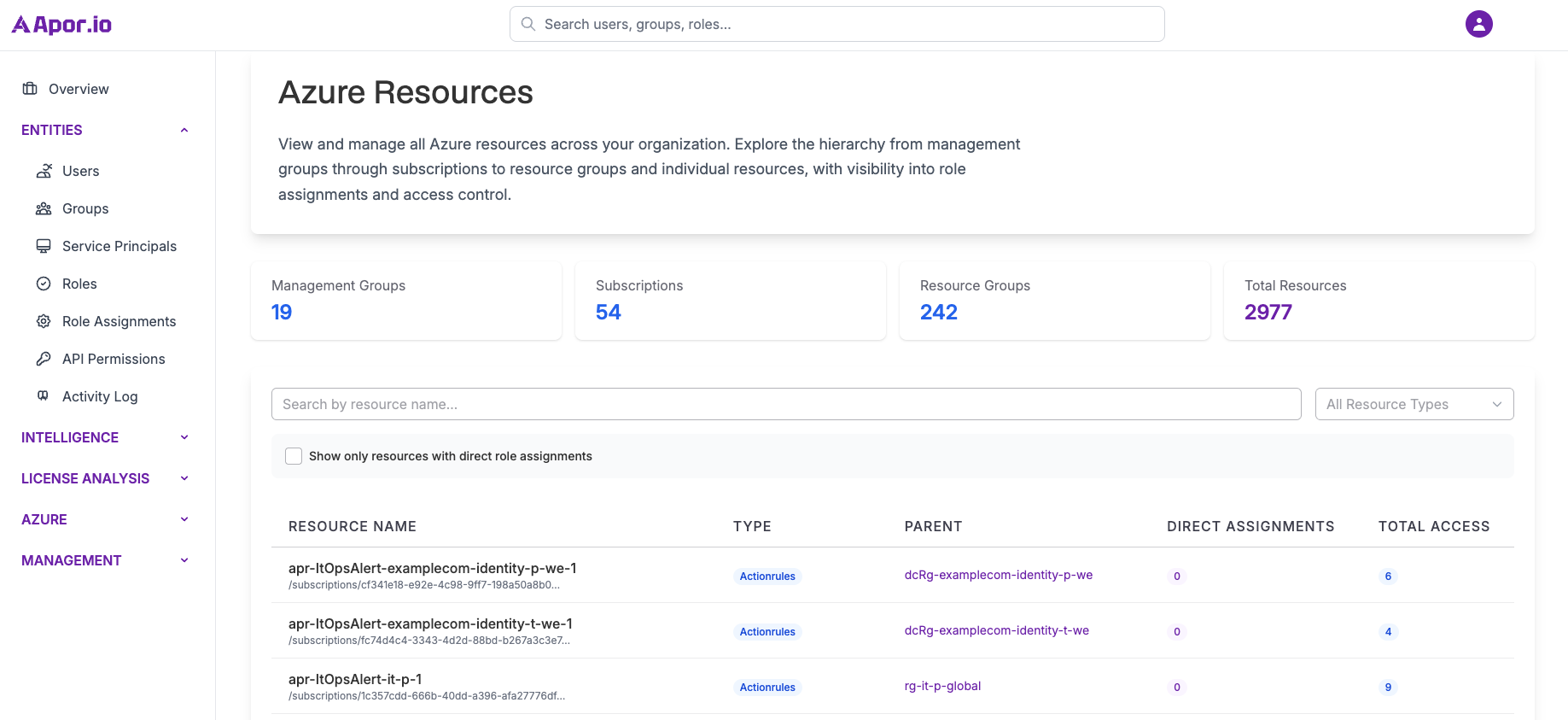
Azure Discovery
Continuously discover and catalog all Azure resources with their associated identities and permissions.
-
Comprehensive Resource Inventory
Discover VMs, storage, databases, and all Azure resources
-
RBAC Role Mapping
Map identity permissions across Azure resources
-
Shadow IT Detection
Identify anomalous resources and access patterns
Ready to Secure Your Identities?
Schedule a personalized demo to see how Aporio can provide complete visibility into your Microsoft Entra ID environment.
Schedule Demo